Productos
Inspiración
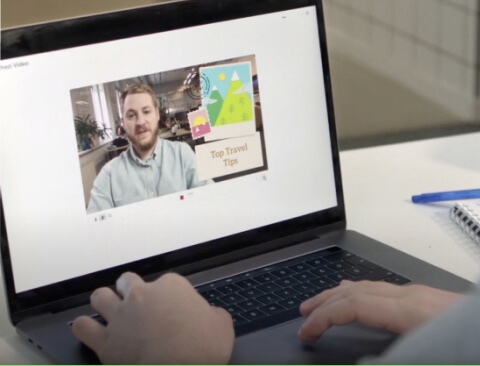
Vídeos recomendados Descubren cómo aprovechan Prezi Video otros usuarios para atraer a su público. Presentaciones reutilizables Consulta algunas de nuestras presentaciones favoritas y cópialas para utilizarlas como plantillas. Infografías reutilizables Personaliza el contenido de estas infografías para crear tus propias obras de arte. Plantillas de presentación Ve con ventaja creando tus propios vídeos, presentaciones o infografías.Soluciones
Negocios
Para marketing Crea mensajes de marketing impactantes y personalizados que atraigan a cualquier audiencia. Para ventas Descubre cómo un toque de personalidad en tu mensaje de ventas mejora las relaciones con los clientes. Para recursos humanos Haz que los materiales importantes sean más atractivos y memorables con Prezi.Recursos
Conectar
Webinars ¿Necesitas ayuda con una presentación, un vídeo o un gráfico? Habla con un experto/a hoy mismo. Blog de Prezi Lee las últimas noticias y consejos de nuestros expertos internos y del sector. Sala de prensa de Prezi Aprende de expertos, personas influyentes y líderes de opinión en nuestros seminarios web y foros.