Termékek
Inspiráció
Ajánlott videók Nézze meg, hogy más felhasználók hogyan teremtenek lebilincselő élményt a közönségeik számára a Prezi Videóval. Újrahasznosítható prezentációk Böngésszen kedvenc prezentációink közül, és másolja őket a sablonként való felhasználásuk érdekében. Újrafelhasználható infografikák Szabja testre ezen infografikák tartalmát, és készítse el saját műalkotásait. Prezentációs sablonok Hatalmas lépéselőnyre tehet szert, amikor saját videóit, prezentációit vagy infografikáit készíti.Megfontolás
Biztonság SOC2-megfelelőséggel rendelkezünk, és rendszereinket alaposan figyeljük az év 365 napján, a hét minden napján, a nap 24 órájában. Ügyfeleink Ismerkedjen meg a különböző ágazatokban tevékenykedő több száz jelentős vállalattal, amelyek a Prezit használják a jobb kommunikáció érdekében.Megoldások
Üzleti
A marketingrészleg számára Hozzon létre hatásos, egyéni márkaarculattal ellátott marketingüzeneteket, amelyek bármilyen közönséget képesek megszólítani. Az értékesítési részleg számára Nézze meg, hogyan teszi jobbá az ügyfélkapcsolatot, ha személyesebb hangnemet üt meg az értékesítési üzenetében. A HR részleg számára Tegye lebilincselőbbé és emlékezetesebbé a fontos anyagokat a Prezivel.Segédanyagok
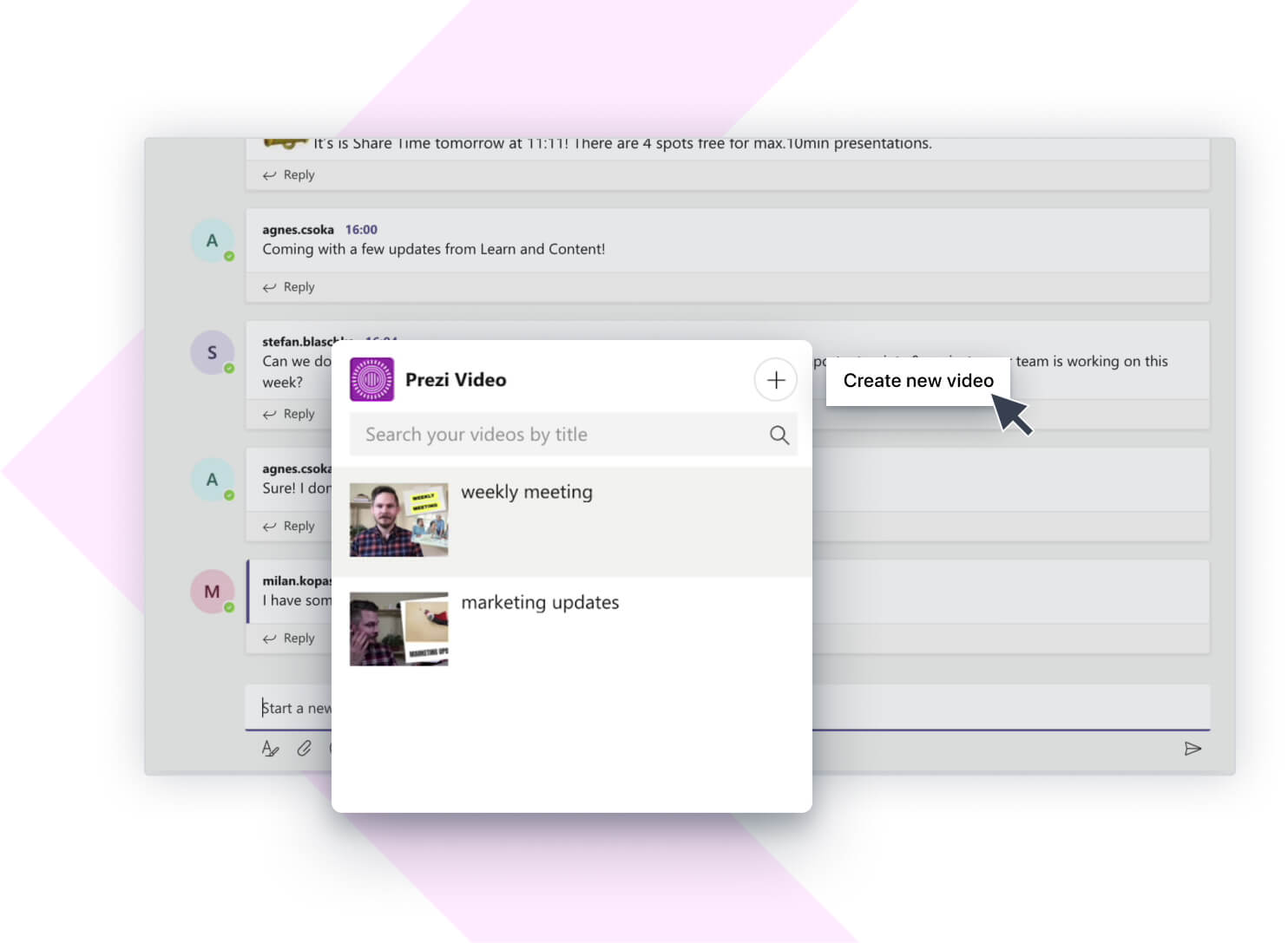
Csatlakoztatás
Webináriumok Segítségre van szüksége egy prezentációval, videóval vagy grafikával? Beszéljen egy szakértővel még ma. Prezi blog Olvassa el a legfrissebb híreket és tippeket a belsős és iparági szakértőinktől. Prezi hírközpont Webináriumainkon és fórumainkon szakértőktől, influencerektől és véleményvezérektől tanulhat.
Mozgó, ráközelítéseket alkalmazó prezentációkat hozhat létre, melyek megragadják és meg is tartják az emberek figyelmét.

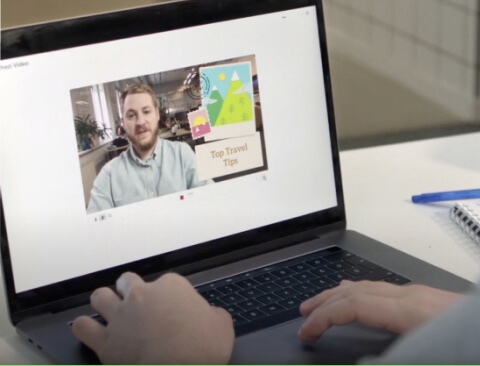
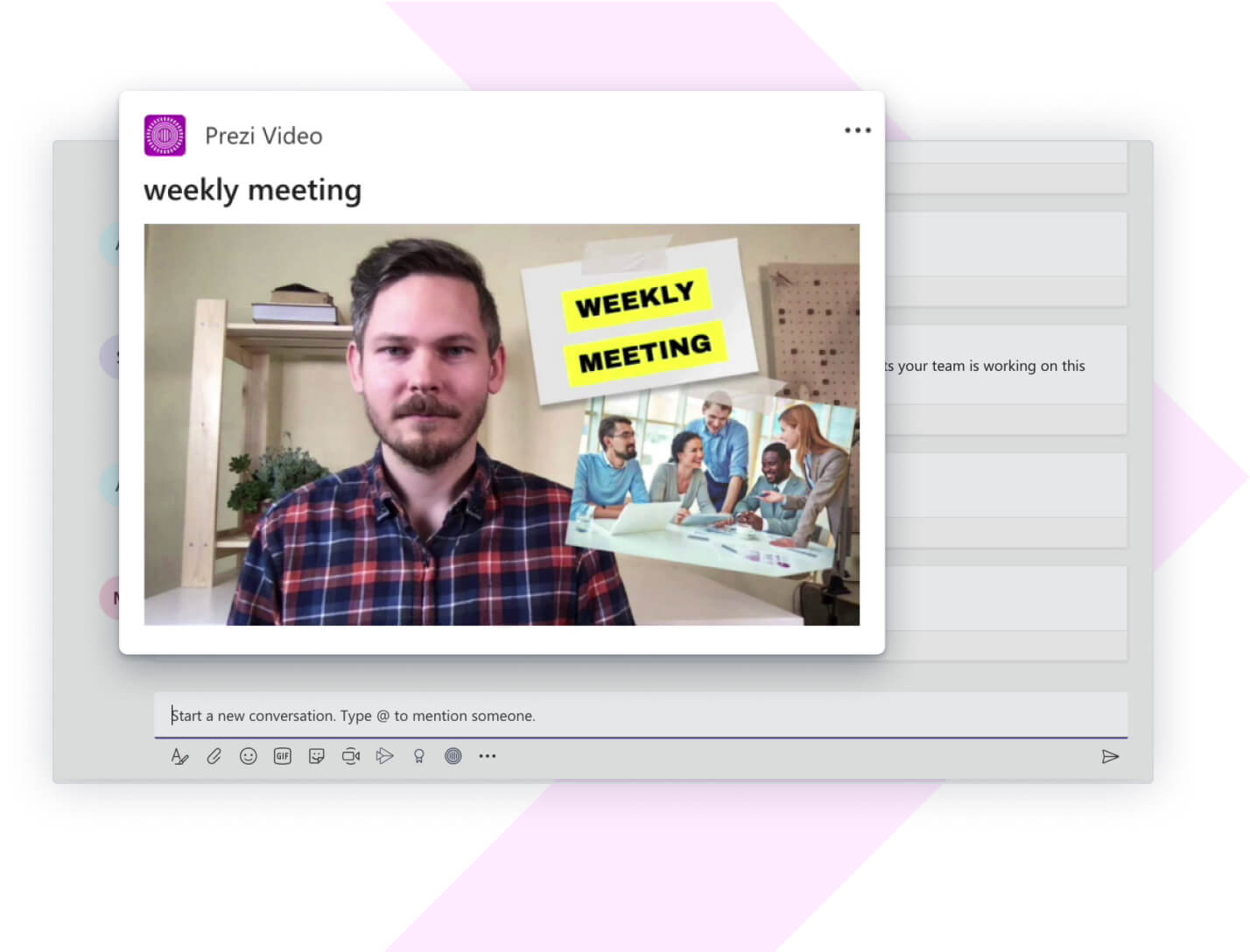
Látható maradhat közvetlenül a tartalmai mellett, miközben prezentációt tart a közönségnek.

Lenyűgöző, interaktív diagramokat, jelentéseket, térképeket, infografikákat és egyebeket készíthet.